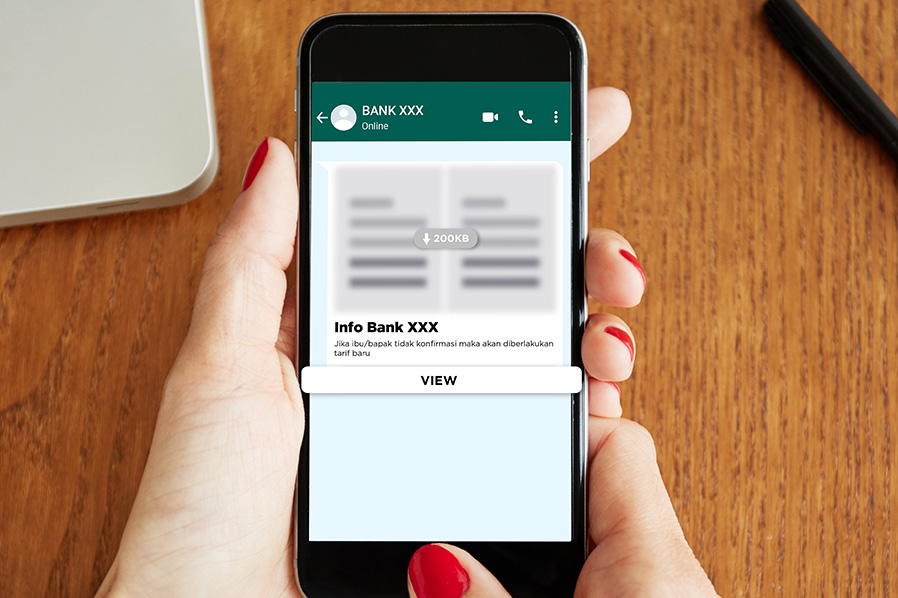
More and more diverse modes of customer data theft are difficult to guess. Following the APK and PDF file fraud modes, which were widely rampant, a new fraud mode emerges that also utilizes WhatsApp chat with the addition of a ‘view’ action button or other button(s) below it.
When click on the button, there are two possibilities.
First, a web form will appear asking for banking data/personal data, and if you fill it in, all the credentials will be sent to the criminal’s server and misused.
Secondly, you could be clicking on a malicious APK application that if installed and granted ‘permission’ contains malware that can infect your device and steal your sensitive information to be misused by the fraudster.
Such sensitive data will be used by the criminals to drain the victim’s account. This is why we need to be more vigilant to avoid this kind of fraud and data theft.
Tips if you encounter a fraudulent chant mode with a ‘View’ action button
It is possible for you to be the target of this type of crime mode. Here are tips to avoid fraud mode that uses the ‘view’ action button of other buttons.
1. Ignore messages from unknown senders
The first and most effective tip is to ignore messages from senders claiming to be on behalf of the bank. Especially when they call using a personal number. You can be sure that they have hidden intentions.
Banks will only make announcements on official social media numbers/accounts if they have new information for customers. Do not trust messages or information that comes from parties on behalf of the bank.
2. Avoid clicking the‘view’ button and filling in the data
Avoid opening or clicking the ‘view’ button or other buttons to see the contents. Especially if it is clearly from an official bank number/source, especially BCA. If you have already clicked it, avoid filling out the web form in it. Immediately exit the website or microsite that opens from the page. If it is a document, delete the document that has been downloaded on the cellphone. This will save the data stored on the device from viruses that have entered along with the document.
3. Block the contact number
The next step is to block the sender’s contact number. This step will prevent the number from sending messages to your mobile phone number. That way, you will be free from further data theft attempts.
Even so, fraudsters may change their number and do it all over again. Do the same steps by blocking the contact number of the malicious sender.
4. Delete messages
For safety precautions, you need to delete the message from the conversation list on WhatsApp. Even if it has been blocked, you can still open messages that have been sent before. This also opens up the opportunity to accidentally open the virus document. You can also use the automatic chat deletion service so that no conversation history is stored.
5. Manage mobile banking passwords properly
To reduce the risk of data theft, manage your mobile banking passwords properly. Create a strong password and change it regularly. Avoid using the same password for all banking accounts/applications.
Tips if you have already clicked on the 'View' button and filled out data/installed files
If you have already clicked ‘view’ and then filled in data or installed an application/APK file, in which the file is opened/executed, the following steps are recommended.
- Immediately uninstall the APK file that is the source of the malware.
- Change all passwords for mobile banking apps on your device. This step is done to reduce the risk of data theft.
- Report this mode of fraud and data theft to HaloBCA at 1500888 or through the haloBCA app for further handling. This will help the bank eradicate data theft cases and prevent it from happening to other people.
Those are the steps to avoid data theft frauds through the action button on WhatsApp. Find out information on other banking modes at #Awasmodus. By knowing more, you can be more aware of the fraud modes used by the fraudsters.